- Debrief - The undercover dispatch
- Posts
- December Undercover: How to Infiltrate and Hack White Supremacist Websites
December Undercover: How to Infiltrate and Hack White Supremacist Websites
Inside the systems of hate, using the tools of hacking and undercover journalism.
As promised, here we are with the first issue of Debrief in 2026. The first days of the year, from a geopolitical and news perspective, have been dramatic. The story we tell today may appear lighter compared to recent events, but it is in fact highly revealing.
It tells the story of a German journalist and hacktivist who infiltrated three white supremacist and extremist social networks for months, reconstructing how they worked, who ran them, and the networks of users behind them. An operation that culminated a few days ago in a public and spectacular exfiltration that exposed the main online gathering places of neo-Nazis.
This issue is written by Luigi and edited by Sacha.
In This Issue of Debrief:
The Pink Power Ranger with root access
Little is known about her, except that she is a German activist, hacker, and investigative journalist who describes herself as an “old-school anarchist.” In recent months she has collaborated with journalists Eva Hoffmann and Christian Fuchs of the weekly Die Zeit to investigate supremacist platforms also based in Germany, phenomena that may appear niche, yet are capable of spreading racist and violent ideas in a pervasive way.
Not much else is known about this hacktivist, apart from the pseudonym she chose to sign her actions: Martha Root. A name that is already a statement of intent: it refers to the pacifist and anti-racist activist of the same name who lived between the late nineteenth and early twentieth centuries, while also functioning as a kind of technical inside joke. In computing, “root” is the highest level of access, total control over a system. In short, her nickname alone hinted at her program: using radical anti-racism to gain full access to the infrastructures that promote hate.
Beyond this, it is known that Martha Root has a strong passion for the Power Rangers, particularly the pink one. And it was precisely while wearing the superhero uniform that, at the Chaos Communication Congress 2025, an international hackers’ conference, Root concluded her talk by deleting the servers of the websites WhiteDate, WhiteChild, and WhiteDeal. Three sites reserved exclusively for white users, designed to function as a kind of Tinder and LinkedIn for neo-Nazis. They were conceived to translate the ideology of white supremacy into everyday life: finding a soulmate, selecting the best sperm or egg donor to reproduce, and building professional networks among supremacists.
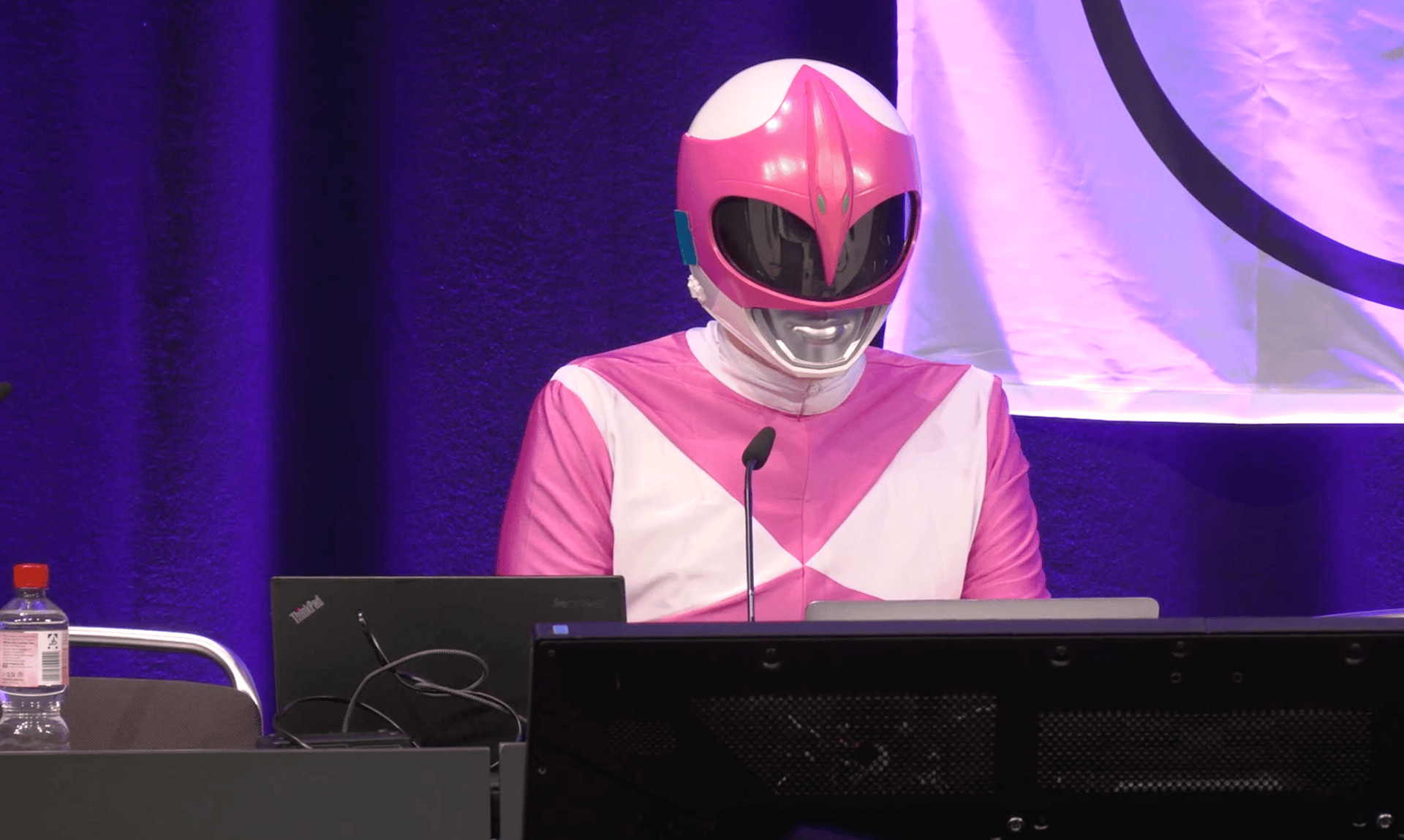
Martha Root during her talk at the CCC
To achieve her goal, Martha Root created fake profiles on WhiteDate and related platforms using chatbots deployed as artificial-intelligence-based female profiles, capable of simulating supremacist ideology in an apparently credible way and of easily passing registration checks, even being certified as “white.”
She explained that she infiltrated these platforms for months, letting the chatbots spend weeks conversing with neo-Nazi users, so much so that some of them reportedly even fell in love with her fake profiles, while she collected data on her targets. By combining techniques of social engineering and OSINT (open source intelligence), the hacker managed to reconstruct the identity of the platforms’ alleged founder, a musician who had converted to neo-Nazism. Not only that: she also uncovered their real, and rather weak, technical infrastructure.
A digital ecosystem for white supremacy
But what exactly were these platforms? WhiteDate, nicknamed the “Tinder for Nazis,” was a dating site aimed at white supremacists. According to an investigation by Die Zeit, it was founded by a German woman convinced of the existence of a “white genocide.” She claimed that only 6% of people in the world are truly white and that “we have the right to preserve ourselves as a race.” Based on figures presented at the Chaos Communication Congress, WhiteDate had around 8,000 users, 86% of them men.
WhiteChild, on the other hand, was a “genetic” matchmaking platform for white supremacists, designed to connect sperm and egg donors on the basis of racial criteria. WhiteDeal functioned instead as a services and professional networking site reserved for white users with a racist ideology. It offered job connections within white-centric networks, potentially usable to place extremist militants inside “friendly” companies. All three platforms openly promoted racial supremacy and white nationalism, sharing not only the same ideological framework and naming scheme, but also the same operator. Their technical infrastructures were extremely rudimentary, and therefore easy to bypass, breach, and expose to the public.
By exploiting the technical vulnerabilities present on the sites, Martha Root discovered that the entire WhiteDate database could be downloaded simply by adding “/download-all-users/” to the site’s URL. In a short time, she obtained all the available data: sensitive information such as age, profile photos, political beliefs, and images containing detailed metadata, including GPS coordinates. Part of this material was published on the satirical website okstupid.lol, a kind of parody of OkCupid, the well-known dating app.
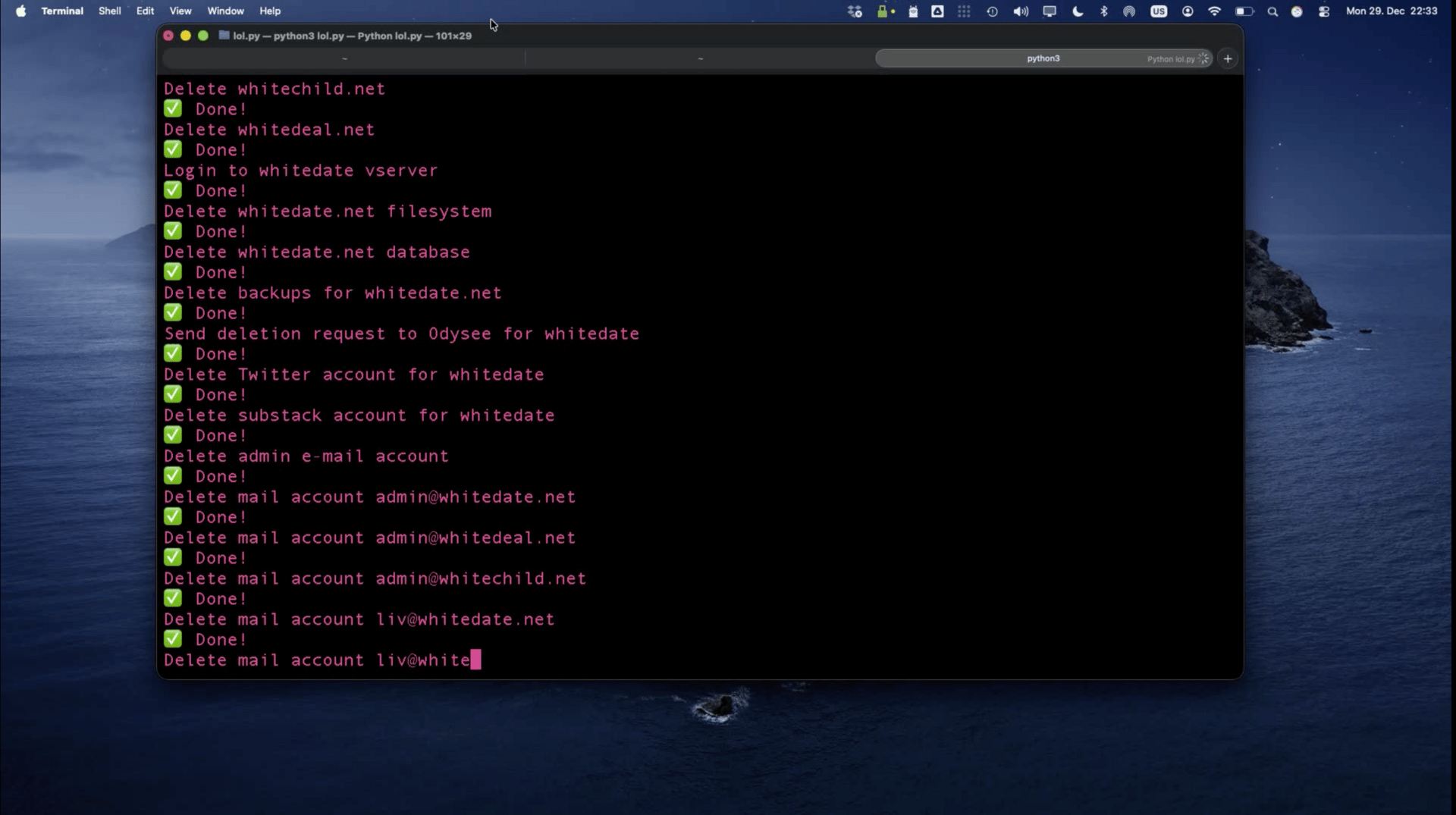
At the end of her talk at the Chaos Communication Congress, Root then executed a script live on stage that deleted the databases and backups of WhiteDate, WhiteChild, and WhiteDeal. The action was met with long applause from the hacker audience. The administrator of the sites reacted by calling the operation “cyber-terrorism” on X and threatening legal action.
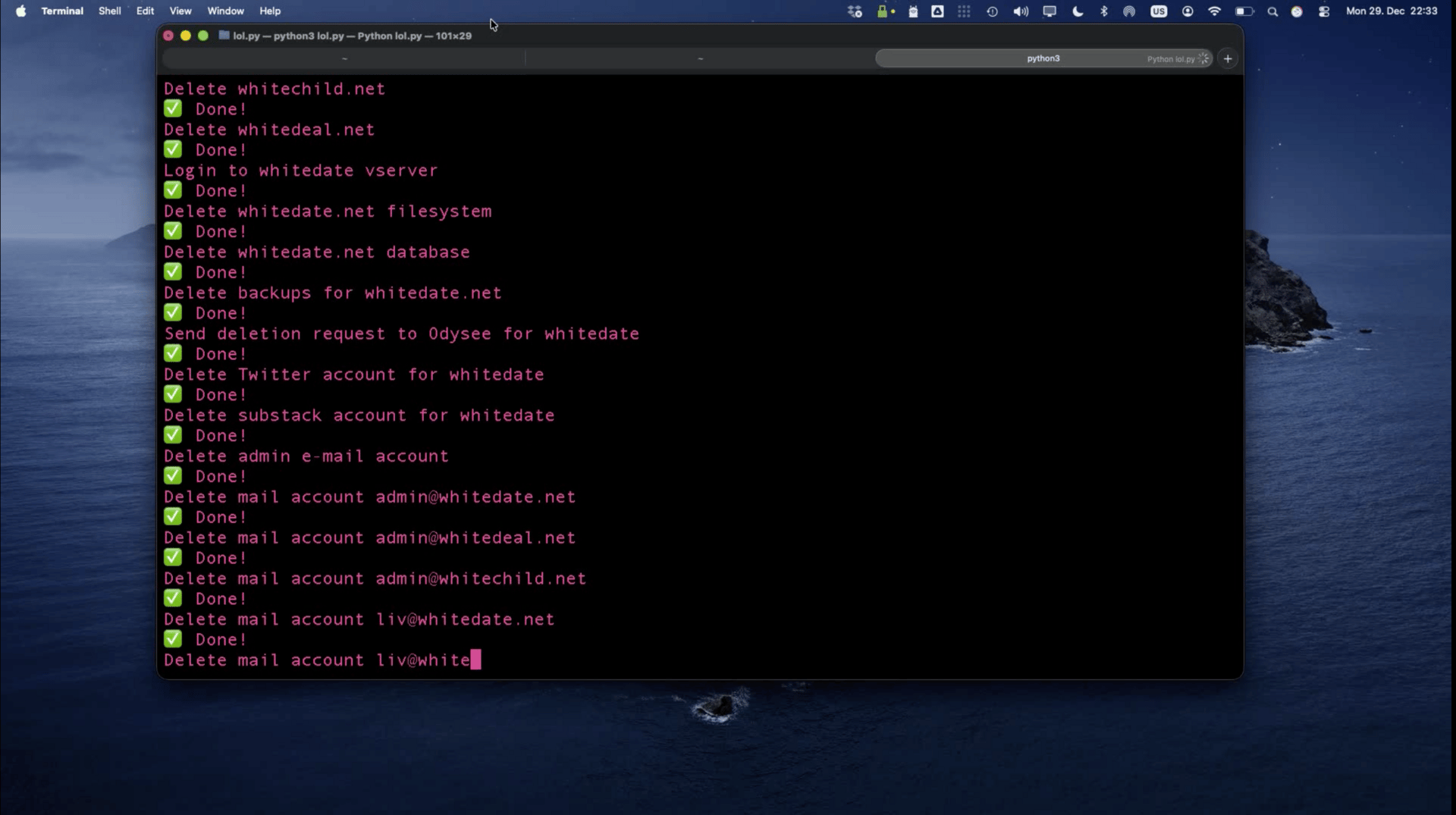
The moment Martha Root wipes out the entire white supremacist ecosystem
Meanwhile, the unusual appearance of Martha Root dressed as a Power Ranger quickly became iconic, spreading across the internet in the form of memes. Yet despite its ironic dimension, her action demonstrates how often the boundaries between hacking and undercover journalism are in fact very thin: both rely on the ability to enter a protected system by exploiting technical and human vulnerabilities, to bring information out into the open that can be useful to the public.
Until the next Debrief,
Luigi and Sacha
If you've come across an undercover investigation you think we should feature, share it with us here:
👉 https://forms.gle/1JbqMBJUfoRU9MBp7
If you have suggestions, questions, tips (or insults), drop us a line at:
👉 [email protected]
If you enjoyed this newsletter, pass it along to your friends using this link:
👉 https://debrief-newsletter.beehiiv.com/
Follow us on Instagram, occasionally we'll upload content different from the newsletter:
👉 https://www.instagram.com/debrief_undercover/
We've also launched a podcast featuring interviews with the authors of memorable undercover investigations:
👉 https://open.spotify.com/show
And if that's still not enough, join our Telegram channel, where we can keep the conversation going:
👉 https://t.me/debrief_undercover
Reply